Applied
Cryptography
Cryptography serves as a building block for security. Cryptography is much more than encryption/decryption. It is also used for validating the data integrity, managin keys, enforcing the policy, etc.
At Bach Khoa Cyber Security Center, we have developed several solutions such as key management (KMS), identify and access management systems (IAM), which can provide user federation, strong authentication, fine-grained authorization.
Network Security
Security of the networks refers to the operation of protecting devices and systems that are connected to the network. Sound security controls are recommended for organizations to protect their network, proprietary information, and reputation.
At Back Khoa Cyber Security Center, we are working to advance the state-of-the-art security techniques using both hardware and software-based methods. We have developed a range of products, including firewall, intrusion detection and prevention system (IDPS), virtual private network (VPN), unified threat management (UTM), security information and event management (SIEM), all towards ensuring connected devices and systems remain safe.
Internet of Things
Security
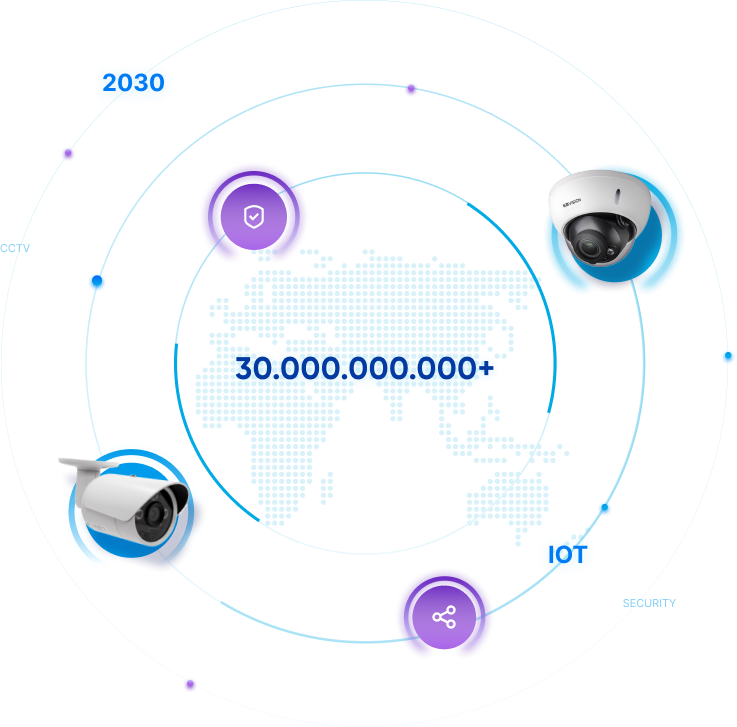
The internet of things promises to connect everything form CCTV cameras, embedded systems, smart home products. It iss expected that by 2030 there will be some +30 billion connected devices worldwide. This growth however comes with many challenges related to privacy and security.
Ensuring the Internet of things secure has been a main research area at Back Khoa Cyber Security Center over the past decade. See our patented DASCAM products for more detailed.
Machine Learning
for Security
Machine Learning (ML) has become a vital technology for cyber security. At Back Khoa Cyber Security Center, we have researchers working on two topics, i.e., ML for security and security of ML.
The research is being conducted and tested in different applications ranging from biometric recognition to systems that can detect malwares and analyze malicious patterns.
We believe that ML can make security simpler, proactive, and effective.

